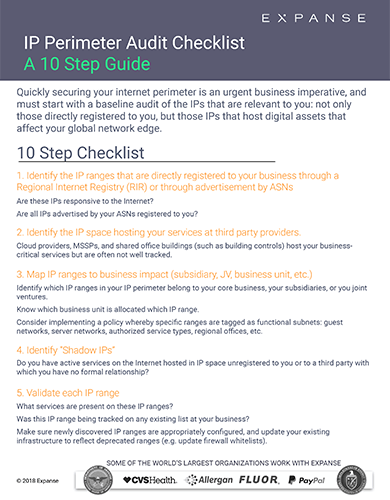
Quickly securing your internet perimeter is an urgent business imperative, and must start with a baseline audit of the IPs that are relevant to you: not only those directly registered to you, but those IPs that host digital assets that affect your data perimeter.
Download this 10-step checklist to get inside advice on simple steps to identify and secure your IP Perimeter.

